[ad_1]
Hardly ever do cybercriminal gangs that deploy ransomware acquire the preliminary entry to the goal themselves. Extra generally, that entry is bought from a cybercriminal dealer who focuses on buying distant entry credentials — comparable to usernames and passwords wanted to remotely hook up with the goal’s community. On this put up we’ll take a look at the clues left behind by “Babam,” the deal with chosen by a cybercriminal who has offered such entry to ransomware teams on many events over the previous few years.

Because the starting of 2020, Babam has arrange quite a few auctions on the Russian-language cybercrime discussion board Exploit, primarily promoting digital non-public networking (VPN) credentials stolen from numerous corporations. Babam has authored greater than 270 posts since becoming a member of Exploit in 2015, together with dozens of gross sales threads. Nonetheless, none of Babam’s posts on Exploit embody any private info or clues about his identification.
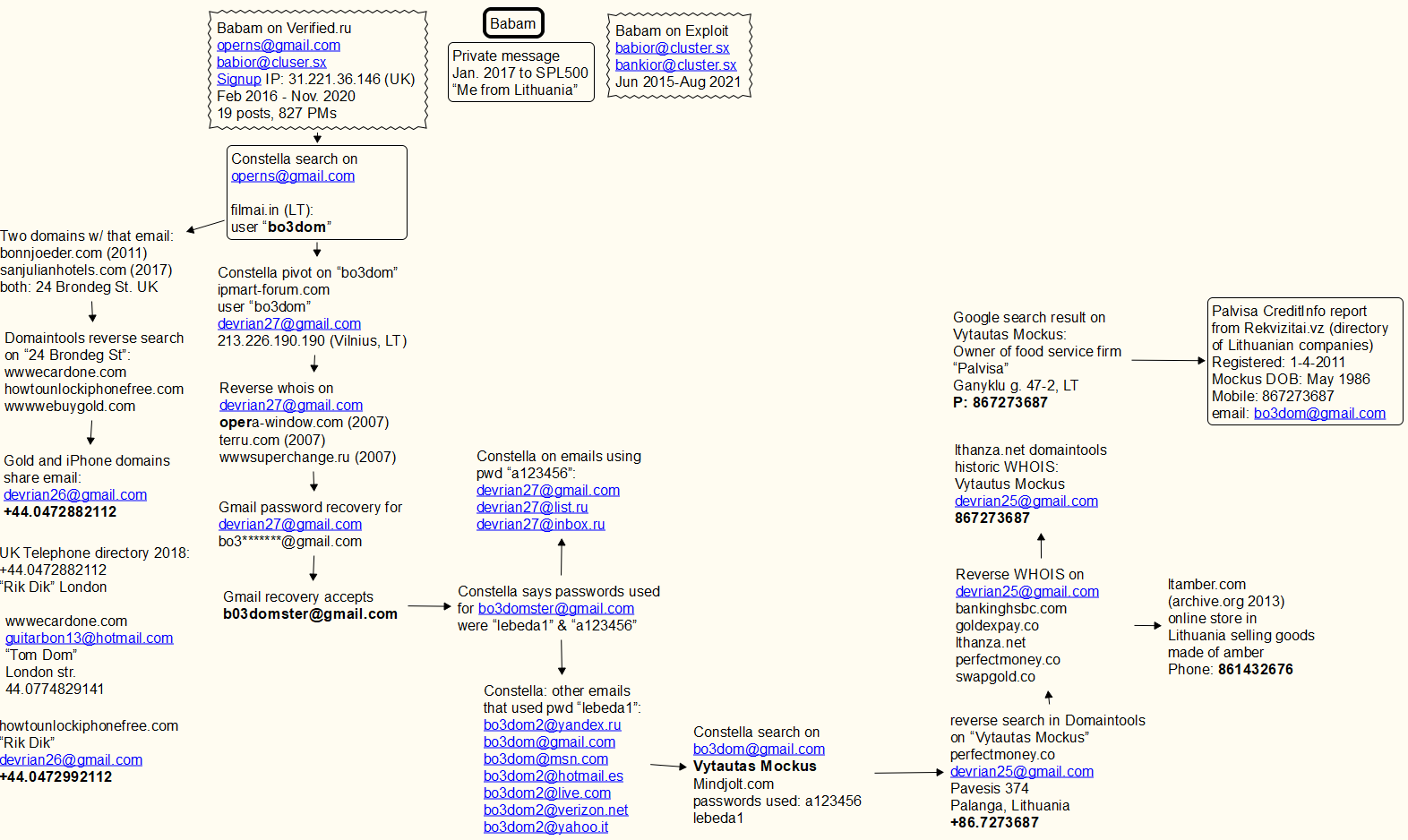
However in February 2016, Babam joined Verified, one other Russian-language crime discussion board. Verified was hacked no less than twice up to now 5 years, and its person database posted on-line. That info reveals that Babam joined Verified utilizing the e-mail tackle “operns@gmail.com.” The newest Verified leak additionally uncovered non-public messages exchanged by discussion board members, together with greater than 800 non-public messages that Babam despatched or obtained on the discussion board through the years.
In early 2017, Babam confided to a different Verified person by way of non-public message that he’s from Lithuania. In just about all of his discussion board posts and personal messages, Babam may be seen speaking in transliterated Russian slightly than through the use of the Cyrillic alphabet. That is widespread amongst cybercriminal actors for whom Russian just isn’t their native tongue.
Cyber intelligence platform Constella Intelligence instructed KrebsOnSecurity that the operns@gmail.com tackle was utilized in 2016 to register an account at filmai.in, which is a film streaming service catering to Lithuanian audio system. The username related to that account was “bo3dom.”
A reverse WHOIS search by way of DomainTools.com says operns@gmail.com was used to register two domains: bonnjoeder[.]com again in 2011, and sanjulianhotels[.]com (2017). It’s unclear whether or not these domains ever have been on-line, however the road tackle on each data was “24 Brondeg St.” in the UK. [Full disclosure: DomainTools is a frequent advertiser on this website.]
A reverse search at DomainTools on “24 Brondeg St.” reveals one different area: wwwecardone[.]com. Using domains that start with “www” is pretty widespread amongst phishers, and by passive “typosquatting” websites that search to siphon credentials from authentic web sites when individuals mistype a site, comparable to by accident omitting the “.” after typing “www”.

A banner from the homepage of the Russian language cybercrime discussion board Verified.
Looking out DomainTools for the cellphone quantity within the WHOIS data for wwwecardone[.]com — +44.0774829141 — results in a handful of comparable typosquatting domains, together with wwwebuygold[.]com and wwwpexpay[.]com. A special UK cellphone quantity in a newer file for the wwwebuygold[.]com area — 44.0472882112 — is tied to 2 extra domains – howtounlockiphonefree[.]com, and portalsagepay[.]com. All of those domains date again to between 2012 and 2013.
The unique registration data for the iPhone, Sagepay and Gold domains share an e mail tackle: devrian26@gmail.com. A search on the username “bo3dom” utilizing Constella’s service reveals an account at ipmart-forum.com, a now-defunct discussion board involved with IT merchandise, comparable to cellular gadgets, computer systems and on-line gaming. That search reveals the person bo3dom registered at ipmart-forum.com with the e-mail tackle devrian27@gmail.com, and from an Web tackle in Vilnius, Lithuania.
Devrian27@gmail.com was used to register a number of domains, together with wwwsuperchange.ru again in 2008 (discover once more the suspect “www” as a part of the area identify). Gmail’s password restoration perform says the backup e mail tackle for devrian27@gmail.com is bo3*******@gmail.com. Gmail accepts the tackle bo3domster@gmail.com because the restoration e mail for that devrian27 account.
In response to Constella, the bo3domster@gmail.com tackle was uncovered in a number of knowledge breaches through the years, and in every case it used one in every of two passwords: “lebeda1” and “a123456“.
Looking out in Constella for accounts utilizing these passwords reveals a slew of extra “bo3dom” e mail addresses, together with bo3dom@gmail.com. Pivoting on that tackle in Constella reveals that somebody with the identify Vytautas Mockus used it to register an account at mindjolt.com, a web site that includes dozens of easy puzzle video games that guests can play on-line.
Sooner or later, mindjolt.com apparently additionally was hacked, as a result of a replica of its database at Constella says the bo3dom@gmail.com used two passwords at that web site: lebeda1 and a123456.
A reverse WHOIS search on “Vytautas Mockus” at DomainTools reveals the e-mail tackle devrian25@gmail.com was utilized in 2010 to register the area identify perfectmoney[.]co. That is one character off of perfectmoney[.]com, which is an early digital forex that was fairly well-liked with cybercriminals on the time. The cellphone quantity tied to that area registration was “86.7273687“.
A Google seek for “Vytautas Mockus” says there’s an individual by that identify who runs a cellular meals service firm in Lithuania known as “Palvisa.” A report on Palvisa (PDF) bought from Rekvizitai.vz — an official on-line listing of Lithuanian corporations — says Palvisa was established in 2011 by a Vytautaus Mockus, utilizing the cellphone quantity 86.7273687, and the e-mail tackle bo3dom@gmail.com. The report states that Palvisa is lively, however has had no workers apart from its founder.
Reached by way of the bo3dom@gmail.com tackle, the 36-year-old Mr. Mockus expressed mystification as to how his private info wound up in so many data. “I’m not concerned in any crime,” Mockus wrote in reply.
The domains apparently registered by Babam over almost 10 years counsel he began off primarily stealing from different cybercrooks. By 2015, Babam was closely into “carding,” the sale and use of stolen fee card knowledge. By 2020, he’d shifted his focus virtually completely to promoting entry to corporations.
A profile produced by risk intelligence agency Flashpoint says Babam has obtained no less than 4 optimistic suggestions critiques on the Exploit cybercrime discussion board from crooks related to the LockBit ransomware gang.
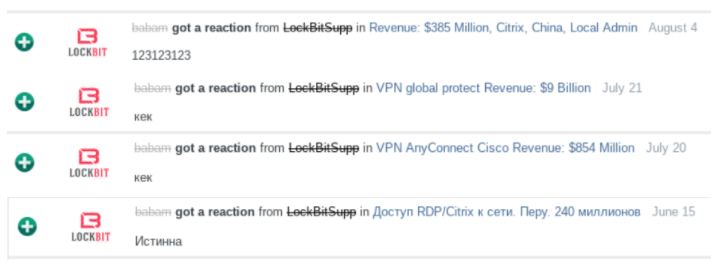
The ransomware collective LockBit giving Babam optimistic suggestions for promoting entry to completely different sufferer organizations. Picture: Flashpoint
In response to Flashpoint, in April 2021 Babam marketed the sale of Citrix credentials for a global firm that’s lively within the area of laboratory testing, inspection and certification, and that has greater than $5 billion in annual revenues and greater than 78,000 workers.
Flashpoint says Babam initially introduced he’d offered the entry, however later reopened the public sale as a result of the potential purchaser backed out of the deal. A number of days later, Babam reposted the public sale, including extra details about the depth of the illicit entry and reducing his asking worth. The entry offered lower than 24 hours later.
“Based mostly on the supplied statistics and delicate supply reporting, Flashpoint analysts assess with excessive confidence that the compromised group was probably Bureau Veritas, a corporation headquartered in France that operates in quite a lot of sectors,” the corporate concluded.
In November, Bureau Veritas acknowledged that it shut down its network in response to a cyber attack. The corporate hasn’t mentioned whether or not the incident concerned ransomware and if that’s the case what pressure of ransomware, however its response to the incident is straight out of the playbook for responding to ransomware assaults. Bureau Veritas has not but responded to requests for remark; its latest public statement on Dec. 2 gives no extra particulars about the reason for the incident.
Flashpoint notes that Babam’s use of transliterated Russian persists on each Exploit and Verified till round March 2020, when he switches over to utilizing largely Cyrillc in his discussion board feedback and gross sales threads. Flashpoint mentioned this could possibly be a sign {that a} completely different particular person began utilizing the Babam account since then, or extra probably that Babam had solely a tenuous grasp of Russian to start with and that his language abilities and confidence improved over time.
Lending credence to the latter principle is that Babam nonetheless makes linguistic errors in his postings that counsel Russian just isn’t his authentic language, Flashpoint discovered.
“Using double “n” in such phrases as “проданно” (right – продано) and “сделанны” (right – сделаны) by the risk actor proves that this fashion of writing just isn’t potential when utilizing machine translation since this is able to not be the proper spelling of the phrase,” Flashpoint analysts wrote.
“A lot of these grammatical errors are sometimes discovered amongst individuals who didn’t obtain enough training at college or if Russian is their second language,” the evaluation continues. “In such instances, when somebody tries to spell a phrase accurately, then accidentally or unknowingly, they overdo the spelling and make these kinds of errors. On the identical time, colloquial speech may be fluent and even native. That is typically typical for an individual who comes from the previous Soviet Union states.”
[ad_2]
Source link