[ad_1]
The U.S. Division of Justice right this moment introduced the arrest of Ukrainian man accused of deploying ransomware on behalf of the REvil ransomware gang, a Russian-speaking cybercriminal collective that has extorted tons of of hundreds of thousands from sufferer organizations. The DOJ additionally stated it had seized $6.1 million in cryptocurrency despatched to a different REvil affiliate, and that the U.S. Division of State is now providing as much as $10 million for the title or location any key REvil leaders, and as much as $5 million for info on REvil associates.
If it sounds unlikely {that a} regular Web person might make hundreds of thousands of {dollars} unmasking the identities of REvil gang members, take coronary heart and think about that the 2 males indicted as half this law enforcement action don’t seem to have carried out a lot to separate their cybercriminal identities from their real-life selves.
Exhibit #1: Yaroslav Vasinskyi, the 22-year-old Ukrainian nationwide accused of being REvil Affiliate #22. Vasinskyi was arrested Oct. 8 in Poland, which maintains an extradition treaty with the US. Prosecutors say Vasinskyi was concerned in quite a lot of REvil ransomware assaults, together with the July 2021 attack in opposition to Kaseya, a Miami-based firm whose merchandise assist system directors handle giant networks remotely.

Yaroslav Vasinksyi’s Vkontakte profile reads “In the event that they inform you nasty issues about me, consider each phrase.”
In accordance with his indictment (PDF), Vasinskyi used quite a lot of hacker handles, together with “Profcomserv” — the nickname behind a web-based service that floods telephone numbers with junk requires a price. Prosecutors say Vasinskyi additionally used the monikers “Yarik45,” and “Yaroslav2468.”
These final two nicknames correspond to accounts on a number of high cybercrime boards approach again in 2013, the place a person named “Yaroslav2468” registered utilizing the e-mail handle yarik45@gmail.com.
That e-mail handle was used to register an account at Vkontakte (the Russian model of Fb/Meta) beneath the profile title of “Yaroslav ‘promote the blood of css’ Vasinskyi.” Vasinskyi’s Vkontakte profile says his present metropolis as of Oct. 3 was Lublin, Poland. Maybe tauntingly, Vasinskyi’s profile web page additionally lists the FBI’s 1-800 tip line as his contact telephone quantity. He’s now in custody in Poland, awaiting extradition to the US.
Exhibit #2: Yevgeniy Igorevich Polyanin, the 28-year-old Russian nationwide who’s alleged to be REvil Affiliate #23. The DOJ stated it seized $6.1 million in funds traceable to alleged ransom funds acquired by Polyanin, and that the defendant had been concerned in REvil ransomware assaults on a number of U.S. sufferer organizations.
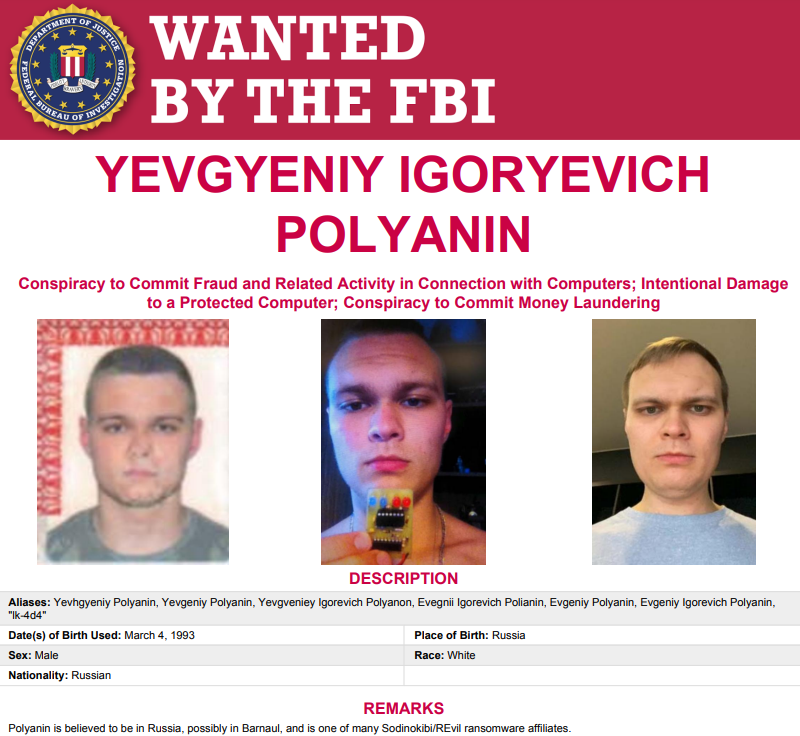
The FBI’s wished poster for Polyanin.
Polyanin’s indictment (PDF) says he additionally favored quite a few hacker handles, together with LK4D4, Damnating, Damn2life, Noolleds, and Antunpitre. A few of these nicknames return greater than a decade on Russian cybercrime boards, lots of which have been hacked and relieved of their person databases through the years.
Amongst these was carder[.]su, and that discussion board’s database says a person by the title “Damnating” registered with the discussion board in 2008 utilizing the e-mail handle damnating@yandex.ru. Positive sufficient, there’s a Vkontakte profile tied to that e-mail handle beneath the title “Yevgeniy ‘rattling’ Polyanin” from Barnaul, a metropolis within the southern Siberian area of Russia.
The obvious lack of any actual operational safety by both of the accused right here is so widespread that it’s hardly exceptional. As exhibited by numerous investigations in my Breadcrumbs story series, I’ve discovered that if a cybercriminal is lively on a number of boards over greater than 10 years, this can be very seemingly that particular person has made a number of errors that make it comparatively simple to attach his discussion board persona to his real-life id.
As I defined earlier this 12 months in The Wages of Password Re-use: Your Money or Your Life, it’s potential in lots of circumstances to make that connection thanks to 2 elements. The most important is password re-use by cybercriminals (sure, crooks are lazy, too). The opposite is that cybercriminal boards, companies, and so on. get hacked nearly as a lot as everybody else on the Web, and after they do their person databases can reveal some very invaluable secrets and techniques and connections.
At the side of right this moment’s REvil motion, the U.S. Division of State stated it was offering a reward of up to $10 million for info resulting in the identification or location of any particular person holding a key management place within the REvil ransomware group. The division stated it was additionally providing a reward of as much as $5 million for info resulting in the arrest and/or conviction in any nation of any particular person conspiring to take part in or trying to take part in a REvil ransomware incident.
I actually like this bounty provide and I hope we see extra similar to it for different ransomware teams. As a result of as we will see from the prosecutions of each Polyanin and Vasinskyi, a whole lot of these guys merely aren’t too arduous to search out. Let the video games start.
[ad_2]
Source link



