[ad_1]
The Conti ransomware associates program seems to have altered its marketing strategy just lately. Organizations contaminated with Conti’s malware who refuse to barter a ransom fee are added to Conti’s sufferer shaming weblog, the place confidential information stolen from victims could also be revealed or bought. However someday over the previous 48 hours, the cybercriminal syndicate up to date its sufferer shaming weblog to point that it’s now promoting entry to most of the organizations it has hacked.
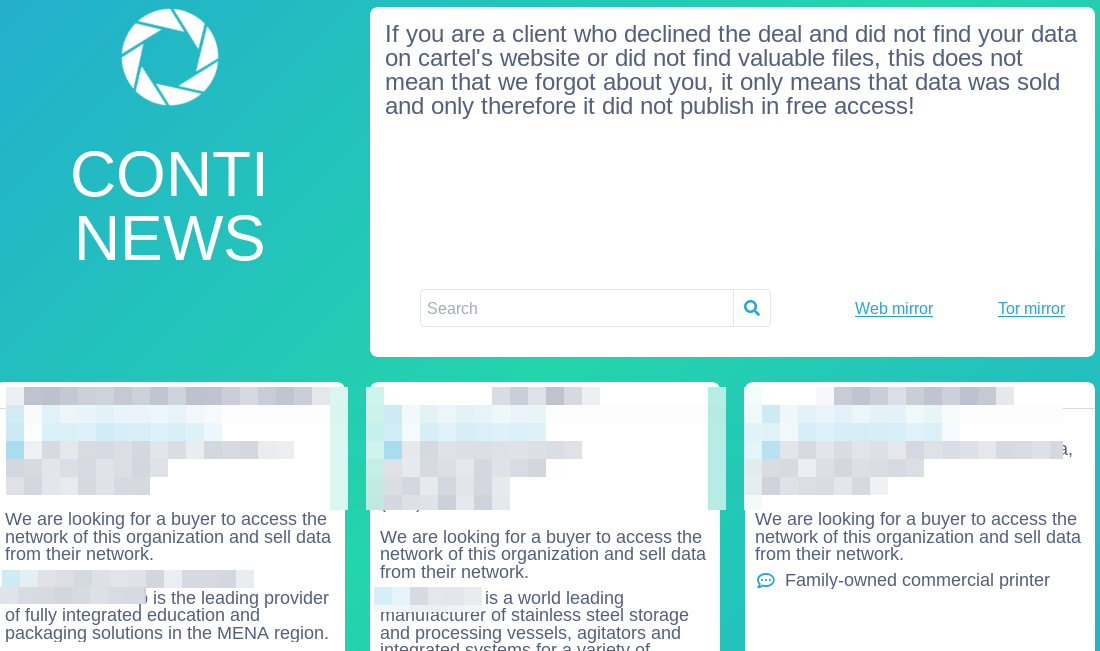
A redacted screenshot of the Conti Information sufferer shaming weblog.
“We’re on the lookout for a purchaser to entry the community of this group and promote knowledge from their community,” reads the confusingly worded message inserted into a number of latest sufferer listings on Conti’s shaming weblog.
It’s unclear what prompted the adjustments, or what Conti hopes to realize from the transfer. It’s additionally not apparent why they’d promote having hacked into firms in the event that they plan on promoting that entry to extract delicate knowledge going ahead. Conti didn’t reply to requests for remark.
“I ponder if they’re about to shut down their operation and need to promote knowledge or entry from an in-progress breach earlier than they do,” mentioned Fabian Wosar, chief expertise officer at laptop safety agency Emsisoft. “However it’s considerably silly to do it that approach as you’ll alert the businesses that they’ve a breach happening.”
The unexplained shift comes as policymakers in the USA and Europe are shifting ahead on efforts to disrupt a few of the prime ransomware gangs. Reuters just lately reported that the U.S. authorities was behind an ongoing hacking operation that penetrated the pc methods of REvil, a ransomware affiliate group that specialists say is about as aggressive and ruthless as Conti in coping with victims. What’s extra, REvil was among the many first ransomware teams to start out promoting its victims’ knowledge.
REvil’s darknet sufferer shaming website stays offline. In response, a consultant for the Conti gang posted a protracted screed on Oct. 22 to a Russian language hacking discussion board denouncing the assault on REvil because the “unilateral, extraterritorial, and bandit-mugging conduct of the USA in world affairs.”
“Is there a regulation, even an American one, even an area one in any county of any of the 50 states, that legitimize such indiscriminate offensive motion?” reads the Conti diatribe. “Is server hacking abruptly authorized in the USA or in any of the US jurisdictions? Suppose there may be such an outrageous regulation that means that you can hack servers in another country. How authorized is that this from the standpoint of the nation whose servers had been attacked? Infrastructure shouldn’t be flying there in area or floating in impartial waters. It is part of somebody’s sovereignty.”
Conti’s obvious new course could also be little greater than one other ploy to convey sufferer firms to the negotiating desk, as in “pay up or somebody pays to your knowledge or long-term distress when you don’t.”
Or possibly one thing simply obtained misplaced within the translation from Russian (Conti’s weblog is revealed in English). However by shifting from the deployment of ransomware malware towards the sale of stolen knowledge and community entry, Conti could possibly be aligning its operations with many competing ransomware affiliate packages which have just lately centered on extorting firms in exchange for a promise not to publish or sell stolen data.
Nevertheless, as Digital Shadows factors out in a recent ransomware roundup, many ransomware teams are discovering it troublesome to handle data-leak websites, or internet hosting stolen knowledge on the darkish net for obtain.
In spite of everything, when it takes weeks to obtain one sufferer’s knowledge by way of Tor — if certainly the obtain succeeds in any respect — the specter of leaking delicate knowledge as a negotiation tactic loses a few of its menace. It’s additionally a crappy consumer expertise. This has resulted in some ransomware teams exposing knowledge utilizing public file-sharing web sites, that are sooner and extra dependable however will be taken down by way of authorized means fairly shortly.
Knowledge leak websites can also provide investigators a possible solution to infiltrate ransomware gangs, as evidenced by the latest reported compromise of the REvil gang by U.S. authorities.
“On 17 Oct 2021, a consultant of the REvil ransomware gang took it to a Russian-speaking prison discussion board to disclose that their data-leak websites had been ‘hijacked’,” Digital Shadows’ Ivan Righi wrote. “The REvil member defined that an unknown particular person accessed the hidden companies of REvil’s web site’s touchdown web page and weblog utilizing the identical key owned by the builders. The consumer believed that the ransomware gang’s servers had been compromised and the person chargeable for the compromise was ‘on the lookout for’ him.”
A recent report by Mandiant revealed that FIN12 — the group believed to be chargeable for each Conti and the Ryuk ransomware operation — has managed to conduct ransomware assaults in lower than 3 days, in comparison with greater than 12 days for assaults involving knowledge exfiltration.
Seen by way of these figures, maybe Conti is merely in search of to outsource extra of the info exfiltration aspect of the enterprise (for a price, after all) in order that it will probably concentrate on the much less time-intensive however equally worthwhile racket of deploying ransomware.
“As This autumn comes close to, it is going to be fascinating to see if points regarding managing knowledge leak websites will discourage new ransomware teams [from pursuing] the trail of data-leak websites, or what inventive options they may create to work round these points,” Righi concluded. “The Ryuk ransomware group has confirmed itself to stay efficient and a prime participant within the ransomware risk panorama with out the necessity for a data-leak website. In reality, Ryuk has thrived by not needing an information leak website and knowledge exfiltration.”
[ad_2]
Source link



