A 31-year-old Canadian man has been arrested and charged with fraud in reference to quite a few ransomware assaults towards companies, authorities companies and personal residents all through Canada and the US. Canadian authorities describe him as “probably the most prolific cybercriminal we’ve recognized in Canada,” however up to now they’ve launched few different particulars concerning the investigation or the defendant. Helpfully, an e mail deal with and nickname apparently linked to the accused provide some extra clues.
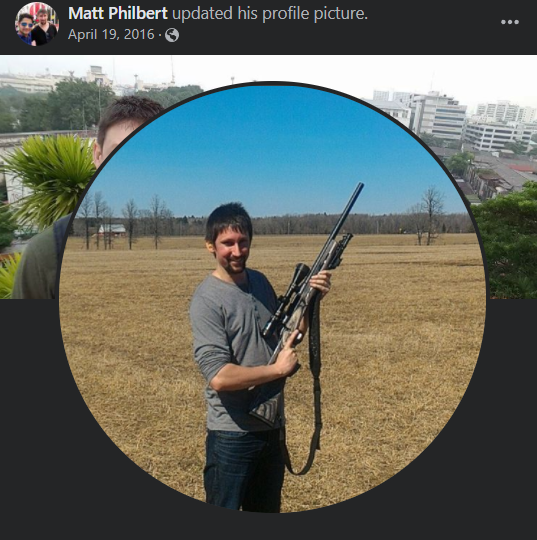
Matthew Philbert, in 2016.
Matthew Philbert of Ottawa, Ontario was charged with fraud and conspiracy in a joint legislation enforcement motion by Canadian and U.S. authorities dubbed “Venture CODA.” The Ontario Provincial Police (OPP) on Tuesday said the investigation started in January 2020 when the U.S. Federal Bureau of Investigation (FBI) contacted them relating to ransomware assaults that have been based mostly in Canada.
“Through the course of this investigation, OPP investigators decided a person was liable for quite a few ransomware assaults affecting companies, authorities companies and personal people all through Canada in addition to cyber-related offenses in the US,” reads an OPP assertion.
“A amount of evidentiary supplies was seized and held for investigation, together with desktop and laptop computer computer systems, a pill, a number of arduous drives, cellphones, a Bitcoin seed phrase and a amount of clean playing cards with magnetic stripes,” the assertion continues.
The U.S. indictment of Philbert (PDF) is unusually sparse, but it surely does cost him with conspiracy, suggesting the defendant was a part of a bunch. In an interview with KrebsOnSecurity, OPP Detective Inspector Matt Watson declined to say whether or not different defendants have been being sought in reference to the investigation, however mentioned the inquiry is ongoing.
“I’ll say this, Philbert is probably the most prolific cybercriminal we’ve recognized so far in Canada,” Watson mentioned. “We’ve recognized in extra of a thousand of his victims. And a variety of these have been small companies that have been simply holding on by their fingernails throughout COVID.”
A DARK CLOUD
There’s a now-dormant Myspace account for a Matthew Philbert from Orleans, a suburb of Ottawa, Ontario. The knowledge tied to the Myspace account matches the age and city of the defendant. The Myspace account was registered beneath the nickname “Darkcloudowner,” and to the e-mail deal with dark_cl0ud6@hotmail.com.
A search in DomainTools on that e mail deal with reveals a number of domains registered to a Matthew Philbert and to the Ottawa telephone quantity 6138999251 [DomainTools is a frequent advertiser on this site]. That very same telephone quantity is tied to a Fb account for a 31-year-old Matthew Philbert from Orleans, who describes himself as a self-employed “broke bitcoin baron.”
Mr. Philbert didn’t reply to a number of requests for remark.
In keeping with cyber intelligence agency Intel 471, that dark_cl0ud6@hotmail.com deal with has been used together with the deal with “DCReavers2” to register consumer accounts on a half-dozen English-language cybercrime boards since 2008, together with Hackforums, Blackhatworld, and Ghostmarket.
Maybe the earliest and most vital cybercrime discussion board DCReavers2 frequented was Darkode, the place he was among the many first two-dozen members. Darkode was taken down in 2015 as part of an FBI investigation sting operation, however screenshots of the neighborhood saved by this writer present that DCReavers2 was already well-known to the Darkode founders when his membership to the discussion board was accepted in Might 2009.
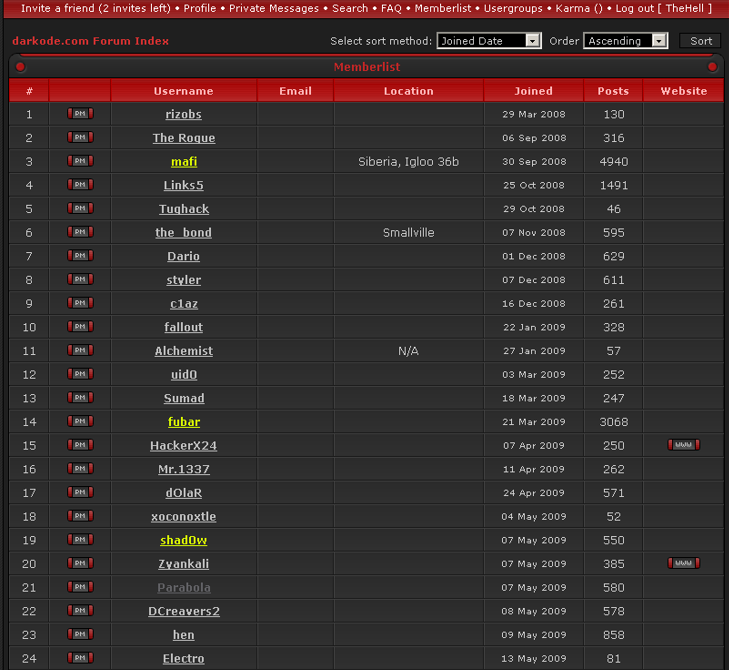
DCReavers2 was simply the twenty second account to register on the Darkode cybercrime discussion board.
Most of DCReavers’s posts on Darkode seem to have been eliminated by discussion board directors early on (possible at DCReavers’ request), however the handful of posts that survived the purge present that greater than a decade in the past DCReavers2 was concerned in operating botnets, or giant collections of hacked computer systems.
“My exploit pack is hosted there with 0 issues,” DCReaver2 says of a shady on-line supplier that one other member requested about in Might 2010.
Looking the Internet on “DCreavers2” brings up a fascinating chat conversation allegedly between DCReavers2 and a person in Australia who was promoting entry to an “exploit kit,” business crimeware designed to be stitched into hacked or malicious websites and exploit a wide range of Internet-browser vulnerabilities for the needs of putting in malware of the client’s selecting.
In that 2009 chat, listed by the researchers behind the web site exposedbotnets.com, DCReavers2 makes use of the Dark_Cl0ud6 e mail deal with and really shares his actual identify as Matthew Philbert. DCReavers2 additionally says his companion makes use of the nickname “The Rogue,” which corresponds to a former Darkode administrator who was the second consumer ever registered on the discussion board (see screenshot above).
In that very same dialog, DCReavers2 discusses managing a botnet constructed on ButterFly Bot. Also called “Mariposa,” ButterFly was a plug-and-play malware pressure that allowed even probably the most novice of would-be cybercriminals to arrange a worldwide operation able to harvesting knowledge from 1000’s of contaminated PCs, and utilizing the enslaved techniques for crippling assaults on Websites. The ButterFly Bot package offered for costs starting from $500 to $2,000.
An commercial for the ButterFly Bot.
The writer of ButterFly Bot — Slovenian hacker Matjaz “Iserdo” Skorjanc — was Darkode’s unique founder again in 2008. Arrested in 2010, Skorjanc was sentenced to just about 5 years in jail for promoting and supporting Mariposa, which was used to compromise thousands and thousands of Microsoft Home windows computer systems.
Upon launch from jail, Skorjanc grew to become chief know-how officer for NiceHash, a cryptocurrency mining service. In December 2017, $52 million value of Bitcoin mysteriously disappeared from NiceHash coffers. In October 2019, Skorjanc was arrested in Germany in response to a U.S.-issued worldwide arrest warrant for his extradition.
The indictment (PDF) tied to Skorjanc’s 2019 arrest additionally names a number of different alleged founding members of Darkode, together with Thomas “Fubar” McCormick, a Massachusetts man who was allegedly one of many final directors of Darkode. Prosecutors say McCormick additionally was a reseller of the Mariposa botnet, the ZeuS banking trojan, and a bot malware he allegedly helped create known as “Ngrbot.” The U.S. federal prosecution towards Skorjanc and McCormick is ongoing.
On the time the FBI dismantled Darkode in 2015, the Justice Division mentioned that out of 800 or so crime boards worldwide, Darkode was probably the most refined English-language discussion board, and that it represented “one of many gravest threats to the integrity of information on computer systems in the US and around the globe.”
A few of Darkode’s core members have been both clients or sellers of assorted “locker” kits, which have been principally web-based exploits that will lock the sufferer’s display right into a webpage spoofing the FBI or Justice Division and warning that victims had been caught accessing baby sexual abuse materials. Victims who agreed to pay a “wonderful” of a number of hundred {dollars} value of GreenDot pay as you go playing cards might then be rid of the PC locker program.

A 2012 gross sales thread on Darkode for Rev Locker.
In some ways, lockers have been the precursors to the fashionable cybercrime scourge we now know as ransomware. The primary motive lockers by no means took off as an existential risk to organizations worldwide was that there’s solely a lot cash locker customers might moderately demand through GreenDot playing cards.
However with the ascendance and broader acceptance of digital currencies like Bitcoin, instantly felony hackers might begin demanding thousands and thousands of {dollars} from victims. And it stands to motive that a fantastic many Darkode members who have been by no means caught have since transitioned from lockers, exploit kits and GreenDot playing cards to doing what each different self-respecting cybercrook appears to be concerned with nowadays: Locking complete firms and industries for ransomware funds.
One last remark concerning the Philbert indictment: It’s good to see the Canadian authorities working carefully with the FBI on vital cybercrime instances. Certainly, this investigation is exceptional for that reality alone. For years I’ve been questioning aloud why extra American cybercriminals don’t simply transfer to Canada, as a result of traditionally there was virtually no chance that they are going to ever get caught — not to mention prosecuted there. Optimistically, this case would be the begin of one thing new.




















