[ad_1]
Privacy
A primer on how to use this powerful tool for uncovering and connecting information from publicly available sources
22 Jun 2023
•
,
4 min. read

It’s a truism that personal data is a valuable asset for cybercriminals, as it allows them to tailor and otherwise improve their phishing and other social engineering attacks. The wealth and variety of personal data that is available online is leveraged for attacks and scams that target not only people but also companies.
But organizations too can tap into techniques such as Open Source Intelligence (OSINT) that allow them to see their network the way attackers might see it and to gather various kinds of publicly available information about themselves in order to identify their weak points and ultimately enhance their security. One such popular and powerful information-gathering tool is a piece of software called Maltego.
What is Maltego and why use it?
Maltego is a piece of software that allows ethical hackers, penetration testers and other security practitioners to uncover information about people or companies on the internet. It enables them to cross-match data and map out connections between social media profiles, email addresses, phone numbers, locations, professional affiliations and other information. The information is represented in easy-to-digest graphical links and relationship diagrams.
Read also: 5 free OSINT tools for social media
Maltego offers a slew of benefits for various entities, both in the private and public sectors. Cybersecurity practitioners can leverage Maltego for gathering valuable information about threats that might jeopardize the security of a company’s information and infrastructure. Law enforcement agencies can use Maltego to collect valuable data that helps in investigating fraud and gathering digital evidence, among other things.
What type of information can Maltego collect?
The tool’s most-used features are those that let you identify and visualize relationships between what the tool calls entities, such as IP addresses, domain names, e-mails, social media profiles, etc. In addition, Maltego allows you to integrate different sources of information, such as databases, online search tools, APIs, etc.
Even Maltego’s free version fetches a large amount of information, including:
- Network information: Maltego can scan and gather information about network hosts, open ports and protocols used. For example, with Maltego, you can download Shodan within the tool, which allows you to gather more specific information about the network to be analyzed.
- Domain and email information: Maltego can gather information about domains, such as our DNS entries, email logs, and host name logs. It can also gather information about email addresses, domain names, email providers and DNS records.
- Social media information: You can get Maltego to collect various kinds of information from social media, including profiles, posts, friends, followers and connections.
- Information about people and organizations: Maltego can gather information about people or organizations, including their names, addresses, telephone numbers, email addresses, websites and social media profiles.
- Malware information: Maltego can gather information about malware, such as file names, fingerprints, attack patterns and behavior. This helps gather information about threats, making it a handy tool for threat intelligence tasks.
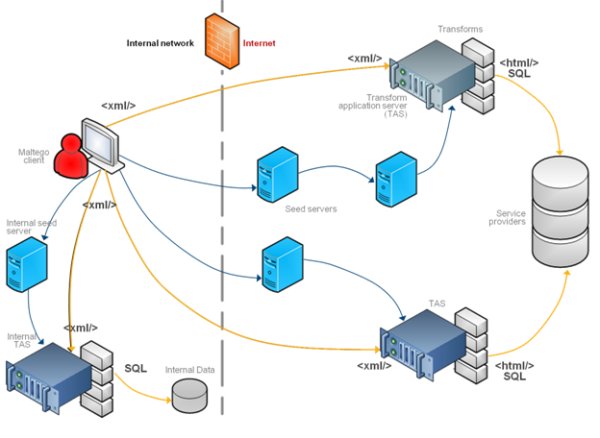
Here’s what happens under the hood:
- The Maltego client sends a request in XML format to seed servers over HTTPS.
- The request from the seed server is sent to transform application servers (TAS) that, in turn, forward it to the service providers.
- The results are sent to the Maltego client.
How to use Maltego
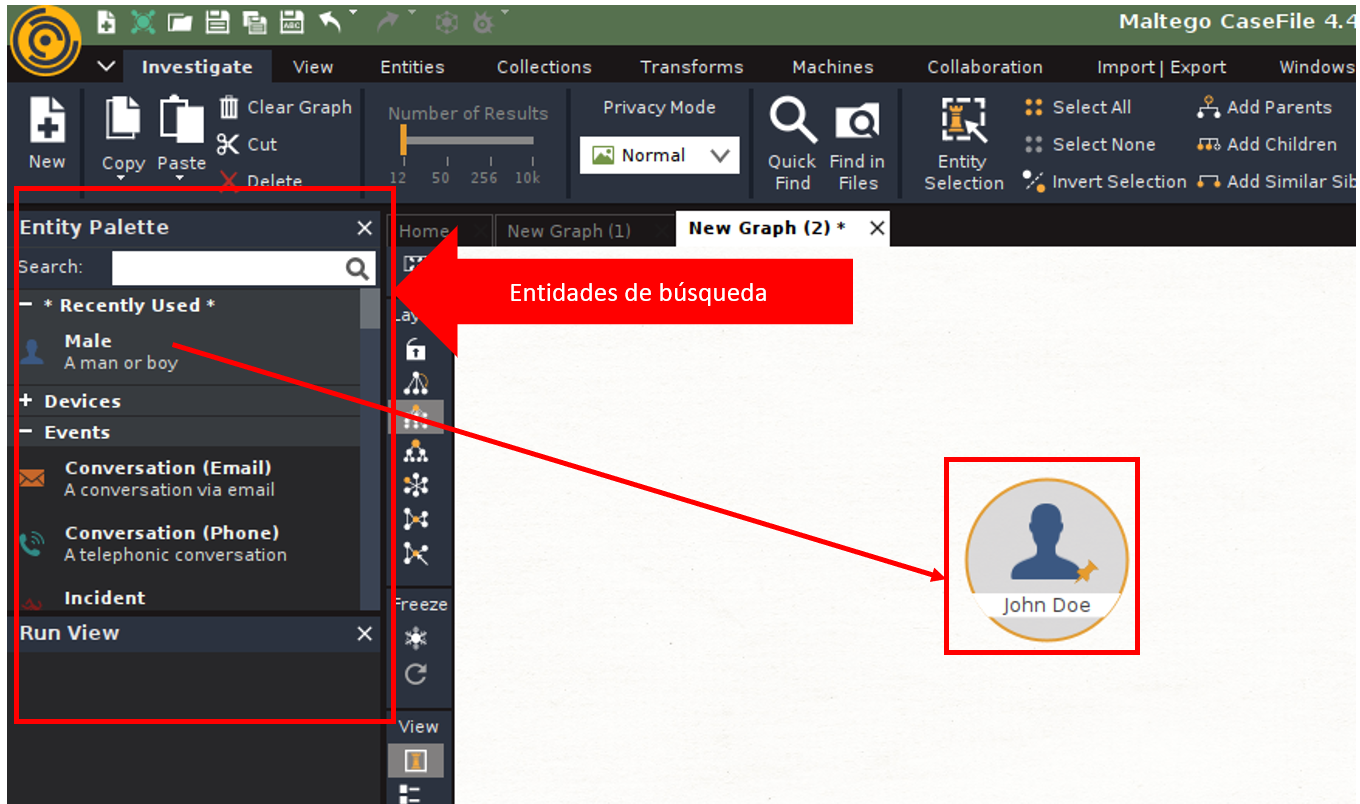
Download and install Maltego on Windows, macOS or Linux and create an account on the tool’s website that will allow you to use the app and the free servers. Once you install the software and sign in, you have to create a new search page and drag the entity there (i.e., the type of search you want to make – in this case, a person) to then run the search and see the results.
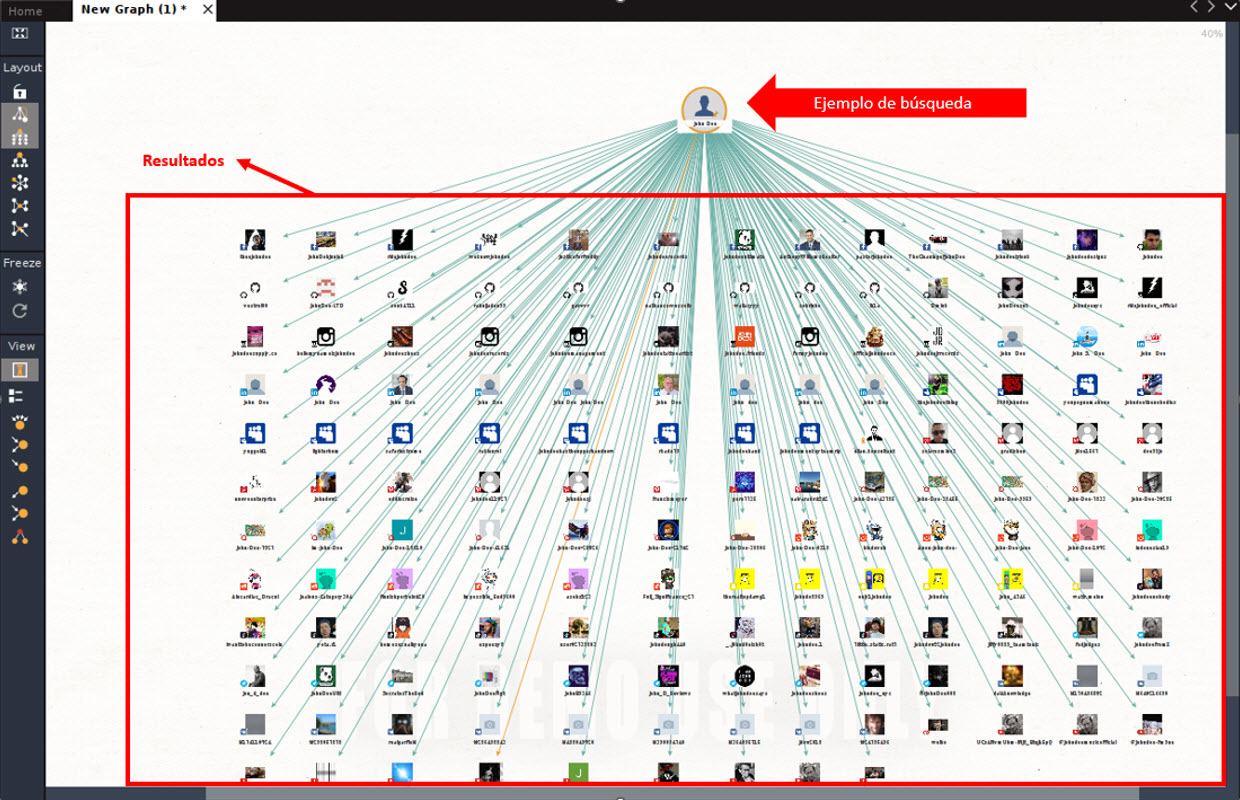
Once you have selected the type of search you want to make, double click on the person icon to access the configuration section and, once you enter the name, just right click on the person icon and select “run transform”. Within this category, there are different subcategories, where you can search for specific information, such as email addresses, IP addresses of a website, etc. In this particular case, we will use the “all transforms” option to search for all possible information in the Internet, so it will quickly start gathering data and the result will be similar to that shown in the image below:
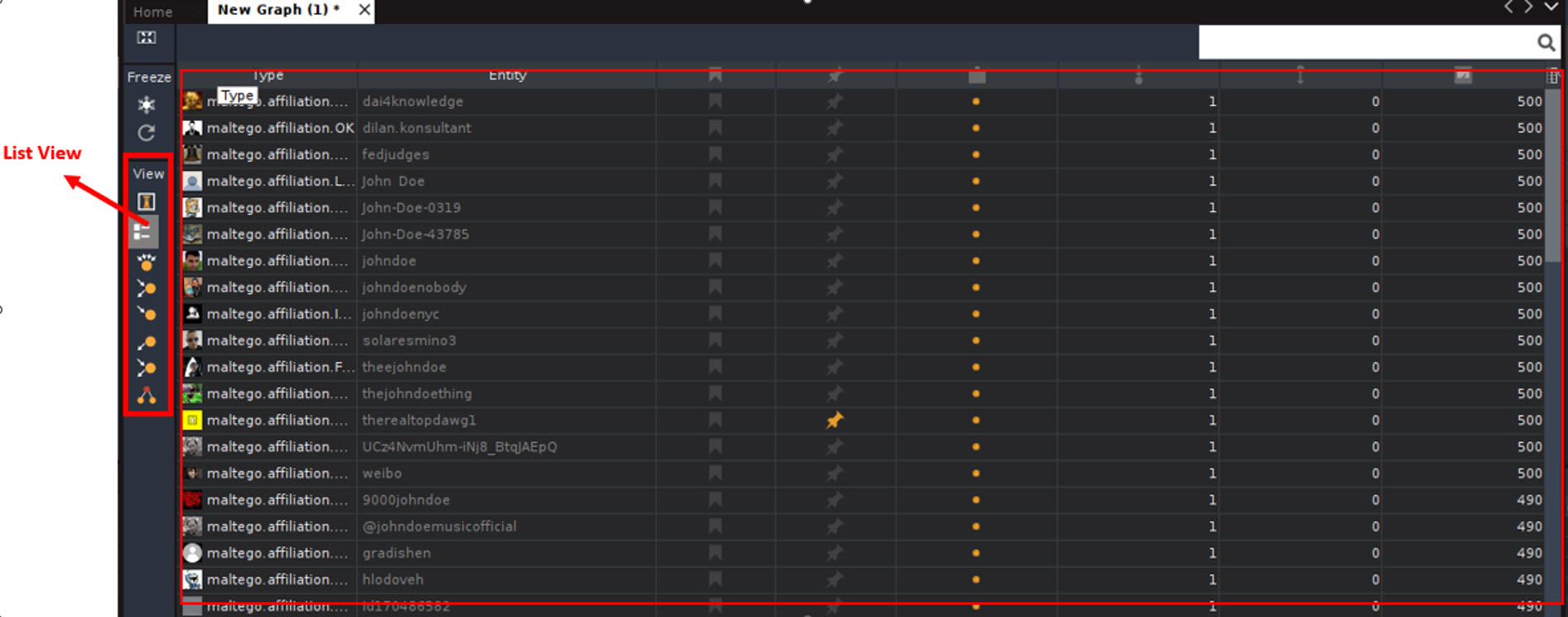
In the screenshot, you can see websites where the name “John Doe” was mentioned or there is information related to it. It is worth mentioning that this tool is so powerful that it may find profiles in Facebook, LinkedIn, Instagram, Tik Tok, Snapchat, Twitter, and Youtube, among others. But that’s not all, as you can also find friends related to this person in social media. To see it in more detail, click on the “List View” button in the “View” lateral bar, where you can see the links and other information.
Conclusion
The information gathered using Maltego can also be used by cybercriminals when deploying their attacks. This is why it’s useful to understand what kind of information a cybercriminal can learn about us or our company and be cognizant of – and possibly decrease – our level of exposure.
It goes without saying that whenever you use an OSINT tool, make sure you are aware of local and national laws and regulations related to the collection and use of information so that you do not commit a crime or violate the privacy of others. Also, when collecting and storing information, it is important to take measures to protect it against possible theft or data breaches.
[ad_2]
Source link