In February, KrebsOnSecurity wrote a couple of novel cybercrime service that helped attackers intercept the one-time passwords (OTPs) that many web sites require as a second authentication issue along with passwords. That service shortly went offline, however new analysis reveals a lot of rivals have since launched bot-based companies that make it comparatively simple for crooks to phish OTPs from targets.

An advert for the OTP interception service/bot “SMSRanger.”
Many web sites now require customers to provide each a password and a numeric code/OTP token despatched through textual content message, or one generated by cell apps like Authy and Google Authenticator. The concept is that even when the person’s password will get stolen, the attacker nonetheless can’t entry the person’s account with out that second issue — i.e. with out entry to the sufferer’s cell system or telephone quantity.
The OTP interception service featured earlier this year — Otp[.]company — marketed a web-based bot designed to trick targets into giving up OTP tokens. This service (and all others talked about on this story) assumes the client already has the goal’s login credentials via some means.
OTP Company prospects would enter a goal’s telephone quantity and identify, after which the service would provoke an automatic telephone name that alerts that particular person about unauthorized exercise on their account. The decision would immediate the goal to enter an OTP token generated by their telephone’s cell app (“for authentication functions”), and that code would then get relayed again to the unhealthy man prospects’ panel on the OTP Company web site.
OTP Company took itself offline inside hours of that story. However in keeping with analysis from cyber intelligence agency Intel 471, a number of new OTP interception companies have emerged to fill that void. And all of them function through Telegram, a cloud-based prompt messaging system.
“Intel 471 has seen an uptick in companies on the cybercrime underground that permit attackers to intercept one-time password (OTP) tokens,” the corporate wrote in a blog post today. “Over the previous few months, we’ve seen actors present entry to companies that decision victims, seem as a reliable name from a selected financial institution and deceive victims into typing an OTP or different verification code right into a cell phone with a view to seize and ship the codes to the operator. Some companies additionally goal different common social media platforms or monetary companies, offering e-mail phishing and SIM swapping capabilities.”
Intel471 says one new Telegram OTP bot known as “SMSRanger” is common as a result of it’s remarkably simple to make use of, and possibly due to the various testimonials posted by prospects who appear proud of its frequent price of success in extracting OTP tokens when the attacker already has the goal’s “fullz,” private data equivalent to Social Safety quantity and date of beginning. From their evaluation:
“Those that pay for entry can use the bot by coming into instructions much like how bots are used on common workforce collaboration software Slack. A easy slash command permits a person to allow varied ‘modes’ — scripts aimed as varied companies — that may goal particular banks, in addition to PayPal, Apple Pay, Google Pay, or a wi-fi service.
As soon as a goal’s telephone quantity has been entered, the bot does the remainder of the work, in the end granting entry to no matter account has been focused. Customers declare that SMSRanger has an efficacy price of about 80% if the sufferer answered the decision and the total data (fullz) the person offered was correct and up to date.”
One other OTP interception service known as SMS Buster requires a tad extra effort from a buyer, Intel 471 explains:
“The bot offers choices to disguise a name to make it seem as a reliable contact from a selected financial institution whereas letting the attackers select to dial from any telephone quantity. From there, an attacker may comply with a script to trick a sufferer into offering delicate particulars equivalent to an ATM private identification quantity (PIN), card verification worth (CVV) and OTP, which may then be despatched to a person’s Telegram account. The bot, which was utilized by attackers concentrating on Canadian victims, offers customers the possibility to launch assaults in French and English.”
These companies are bobbing up as a result of they work and so they’re worthwhile. They usually’re worthwhile as a result of far too many web sites and companies funnel customers towards multi-factor authentication strategies that may be intercepted, spoofed, or misdirected — like SMS-based one-time codes, and even app-generated OTP tokens.
The concept behind true “two-factor authentication” is that the person is required to current two out of three of the next: One thing they’ve (cell units); one thing they know (passwords); or one thing they’re (biometrics). For instance, you current your credentials to a web site, and the positioning prompts you to approve the login through a immediate that pops up in your registered cell system. That’s true two-factor authentication: One thing you’ve, and one thing you understand (and possibly additionally even one thing you might be).
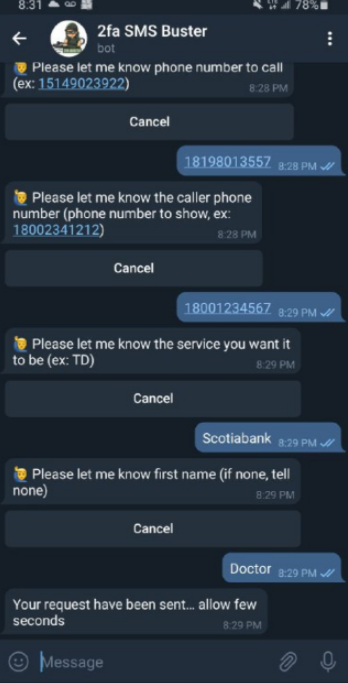
The 2fa SMS Buster bot on Telegram. Picture: Intel 471.
As well as, these so-called “push notification” strategies embrace vital time-based contexts that add safety: They occur immediately after the person submits their credentials; and the chance to approve the push notification expires after a brief interval.
However in so many cases, what websites request is mainly two issues you understand (a password and a one-time code) to be submitted via the identical channel (an internet browser). That is often nonetheless higher than no multi-factor authentication in any respect, however as these companies present there at the moment are loads of choices of circumventing this safety.
I hope these OTP interception companies clarify that it is best to by no means present any data in response to an unsolicited telephone name. It doesn’t matter who claims to be calling: When you didn’t provoke the contact, cling up. Don’t put them on maintain when you name your financial institution; the scammers can get around that, too. Simply cling up. Then you possibly can name your financial institution or whoever else you want.
Sadly, these most probably to fall for these OTP interception schemes are people who find themselves much less skilled with expertise. When you’re the resident or household IT geek and have the power to replace or enhance the multi-factor authentication profiles in your much less tech-savvy associates and family members, that may be a wonderful approach to present you care — and to assist them head off a possible catastrophe by the hands of certainly one of these bot companies.
When was the final time you reviewed your multi-factor settings and choices on the varied web sites entrusted along with your most treasured private and monetary data? It could be price paying a go to to 2fa.directory (previously twofactorauth[.]org) for a checkup.





















