Microsoft on Tuesday issued an emergency software program replace to quash a safety bug that’s been dubbed “PrintNightmare,” a vital vulnerability in all supported variations of Home windows that’s actively being exploited. The repair comes per week forward of Microsoft’s regular month-to-month Patch Tuesday launch, and follows the publishing of exploit code exhibiting would-be attackers the right way to leverage the flaw to interrupt into Home windows computer systems.

At concern is CVE-2021-34527, which entails a flaw within the Home windows Print Spooler service that could possibly be exploited by attackers to run code of their alternative on a goal’s system. Microsoft says it has already detected energetic exploitation of the vulnerability.
Satnam Narang, employees analysis engineer at Tenable, stated Microsoft’s patch warrants pressing consideration due to the vulnerability’s ubiquity throughout organizations and the prospect that attackers may exploit this flaw with the intention to take over a Home windows area controller.
“We count on it’s going to solely be a matter of time earlier than it’s extra broadly integrated into attacker toolkits,” Narang stated. “PrintNightmare will stay a worthwhile exploit for cybercriminals so long as there are unpatched methods on the market, and as we all know, unpatched vulnerabilities have an extended shelf life for attackers.”
In a blog post, Microsoft’s Safety Response Middle stated it was delayed in growing fixes for the vulnerability in Home windows Server 2016, Home windows 10 model 1607, and Home windows Server 2012. The repair additionally apparently features a new characteristic that permits Home windows directors to implement stronger restrictions on the set up of printer software program.
“Previous to putting in the July 6, 2021, and newer Home windows Updates containing protections for CVE-2021-34527, the printer operators’ safety group may set up each signed and unsigned printer drivers on a printer server,” reads Microsoft’s support advisory. “After putting in such updates, delegated admin teams like printer operators can solely set up signed printer drivers. Administrator credentials will likely be required to put in unsigned printer drivers on a printer server going ahead.”
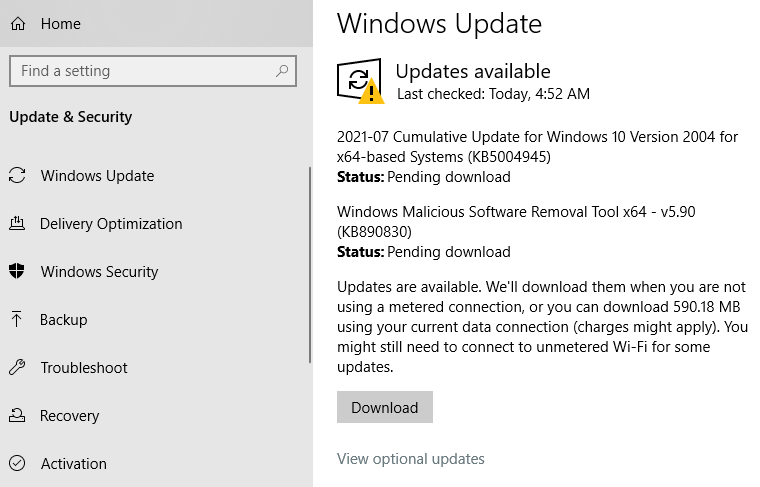
Home windows 10 customers can test for the patch by opening Home windows Replace. Chances are high, it’s going to present what’s pictured within the screenshot beneath — that KB5004945 is accessible for obtain and set up. A reboot will likely be required after set up.
Pleasant reminder: It’s all the time a good suggestion to backup your knowledge earlier than making use of safety updates. Home windows 10 has some built-in tools that will help you try this, both on a per-file/folder foundation or by making a whole and bootable copy of your laborious drive suddenly.
Microsoft’s out-of-band replace might not fully repair the PrinterNightmare vulnerability. Safety researcher Benjamin Delpy posted on Twitter that the exploit nonetheless works on a totally patched Home windows server if the server additionally has Level & Print enabled — a Home windows characteristic that robotically downloads and installs obtainable printer drivers.
Delpy stated it’s frequent for organizations to allow Level & Print utilizing group insurance policies as a result of it permits customers to put in printer updates with out getting approval first from IT.
This publish will likely be up to date if Home windows customers begin reporting any points in making use of the patch.




















