[ad_1]
It occurs on a regular basis: Organizations get hacked as a result of there isn’t an apparent approach for safety researchers to allow them to find out about safety vulnerabilities or knowledge leaks. Or possibly it isn’t fully clear who ought to get the report when distant entry to a company’s inner community is being offered within the cybercrime underground.
In a bid to attenuate these eventualities, a rising variety of main corporations are adopting “Security.txt,” a proposed new Web commonplace that helps organizations describe their vulnerability disclosure practices and preferences.
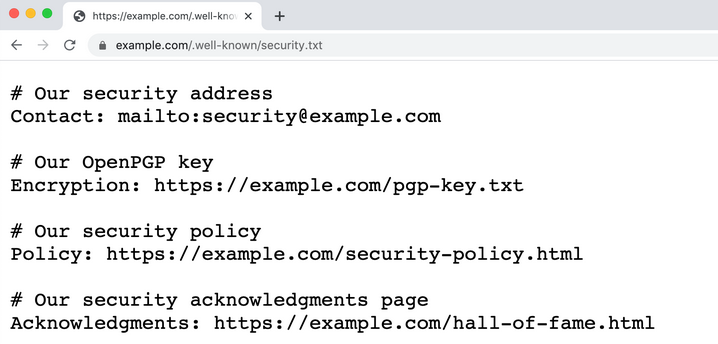
An instance of a safety.txt file. Picture: Securitytxt.org.
The concept behind Safety.txt is simple: The group locations a file referred to as safety.txt in a predictable place — akin to instance.com/safety.txt, or instance.com/.well-known/safety.txt. What’s within the safety.txt file varies considerably, however most embrace hyperlinks to details about the entity’s vulnerability disclosure insurance policies and a contact e-mail tackle.
The security.txt file made accessible by USAA, for instance, consists of hyperlinks to its bug bounty program; an e-mail tackle for disclosing safety associated issues; its public encryption key and vulnerability disclosure coverage; and even a hyperlink to a web page the place USAA thanks researchers who’ve reported vital cybersecurity points.
Different safety.txt disclosures are much less verbose, as within the case of HCA Healthcare, which lists a contact e-mail tackle, and a hyperlink to HCA’s “accountable disclosure” insurance policies. Like USAA and plenty of different organizations which have printed safety.txt information, HCA Healthcare additionally features a hyperlink to details about IT safety job openings on the firm.
Having a safety.txt file could make it simpler for organizations to reply to energetic safety threats. For instance, simply this morning a trusted supply forwarded me the VPN credentials for a serious clothes retailer that had been stolen by malware and made accessible to cybercriminals. Discovering no safety.txt file on the retailer’s website utilizing gotsecuritytxt.com (which checks a website for the presence of this contact file), KrebsonSecurity despatched an alert to its “safety@” e-mail tackle for the retailer’s area.
Many organizations have lengthy unofficially used (if not marketed) the e-mail tackle safety@[companydomain] to simply accept stories about safety incidents or vulnerabilities. Maybe this specific retailer additionally did so at one level, nevertheless my message was returned with a observe saying the e-mail had been blocked. KrebsOnSecurity additionally despatched a message to the retailer’s chief info officer (CIO) — the one individual in a C-level place on the retailer who was in my rapid LinkedIn community. I nonetheless do not know if anybody has learn it.
Though safety.txt will not be but an official Web commonplace as authorised by the Web Engineering Process Pressure (IETF), its fundamental rules have thus far been adopted by no less than eight p.c of the Fortune 100 corporations. In response to a evaluation of the domains for the newest Fortune 100 corporations through gotsecuritytxt.com, these embrace Alphabet, Amazon, Facebook, HCA Healthcare, Kroger, Procter & Gamble, USAA and Walmart.
There could also be one other good cause for consolidating safety contact and vulnerability reporting info in a single, predictable place. Alex Holden, founding father of the Milwaukee-based consulting agency Hold Security, stated it’s not unusual for malicious hackers to expertise issues getting the eye of the correct folks inside the exact same group they’ve simply hacked.
“In instances of ransom, the dangerous guys attempt to contact the corporate with their calls for,” Holden stated. “You don’t have any thought how typically their messages get caught in filters, get deleted, blocked or ignored.”
GET READY TO BE DELUGED
So if safety.txt is so nice, why haven’t extra organizations adopted it but? It appears that evidently organising a safety.txt file tends to ask a relatively excessive quantity of spam. Most of those junk emails come from self-appointed penetration testers who — with none invitation to take action — run automated vulnerability discovery instruments after which submit the ensuing stories in hopes of securing a consulting engagement or a bug bounty fee.
This dynamic was a serious subject of dialogue in these Hacker News threads on safety.txt, whereby plenty of readers associated their expertise of being so flooded with low-quality vulnerability scan stories that it turned troublesome to identify the stories actually value pursuing additional.
Edwin “EdOverflow” Foudil, the co-author of the proposed notification commonplace, acknowledged that junk stories are a serious draw back for organizations that supply up a safety.txt file.
“That is truly acknowledged within the specification itself, and it’s extremely vital to focus on that organizations that implement this are going to get flooded,” Foudil informed KrebsOnSecurity. “One cause bug bounty packages succeed is that they’re mainly a glorified spam filter. However no matter what strategy you employ, you’re going to get inundated with these crappy, sub-par stories.”
Usually these sub-par vulnerability stories come from people who’ve scanned your complete Web for one or two safety vulnerabilities, after which tried to contact all weak organizations directly in some semi-automated style. Fortunately, Foudil stated, many of those nuisance stories could be ignored or grouped by creating filters that search for messages containing key phrases generally present in automated vulnerability scans.
Foudil stated regardless of the spam challenges, he’s heard great suggestions from plenty of universities which have applied safety.txt.
“It’s been an unbelievable success with universities, which are inclined to have a lot of older, legacy programs,” he stated. “In that context, we’ve seen a ton of worthwhile stories.”
Foudil says he’s delighted that eight of the Fortune 100 corporations have already applied safety.txt, although it has not but been authorised as an IETF commonplace. When and if safety.txt is authorised, he hopes to spend extra time selling its advantages.
“I’m not making an attempt to earn money off this factor, which happened after chatting with fairly just a few folks at DEFCON [the annual security conference in Las Vegas] who had been struggling to report safety points to distributors,” Foudil stated. “The principle cause I don’t exit of my strategy to market it now’s as a result of it’s not but an official commonplace.”
Has your group thought of or applied safety.txt? Why or why not? Pontificate within the feedback under.
[ad_2]
Source link



