[ad_1]
The Council’s first benchmark found that 84% of companies have not implemented ethical access, use and outcome policies and procedures per their cloud agendas.
As more and more organizations are moving their data to the cloud, an inaugural study by the data management industry group EDM Council found that many are not doing the move in a coordinated, secure manner.
The Council’s inaugural Cloud Data Management Benchmark Report, based on responses from more than 250 data professionals in more than 30 countries across the globe, found that less than half of the companies it polled trust cloud security and reliability enough to store their more crucial data there.
SEE: Hiring Kit: Database engineer (TechRepublic Premium)
Still, cloud adoption is accelerating quickly, as 2023 research by hiring firm Zippia illustrates: 94% of enterprises currently use cloud services, 92% of businesses have a multi-cloud strategy in place or in the works and 48% of businesses choose to store their most important data in the cloud. The firm also reported that the U.S. public cloud market is projected to reach $258.10 billion by the end of 2023.
Jump to:
Survey shows lack of data management
The EDM Council benchmark study found that among the companies polled, cloud data management is still in the early stages, with respondents characterizing the status of their data management for cloud-deployed data in “Developmental” or “Defined” stages and few at the “Achieved” or “Enhanced” stages of maturity.
The study authors said the management of sensitive data in the cloud; the management of data sovereignty and cross-border movement; and the stewardship of data to ensure ethical access, use and outcomes of data in the cloud should be priorities.
Key findings of the EDM Council’s survey include:
- Ninety-eight percent of companies surveyed would use a verified framework to manage data and its lifecycle in the cloud.
- Eighty-four percent of respondents have not implemented data management policies and procedures as they migrate to the cloud.
- For the 92% of respondents engaged in cloud implementation, their cloud data management capabilities are in the “developmental” stage.
- Most organizations rely heavily on manual processes, which are more labor-intensive and prone to human error.
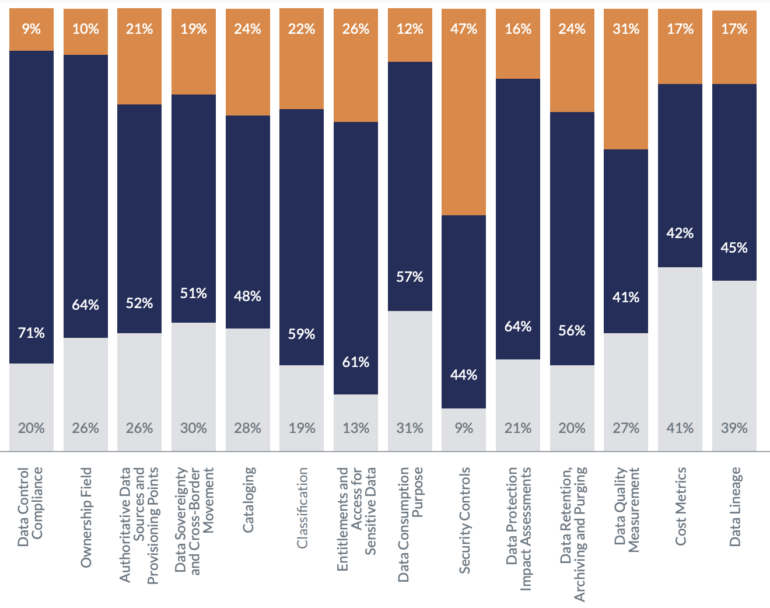
- Levels of automation are low across all categories, with the highest being so-called “security controls” at 47%.
“This cloud-focused analysis complements the EDM Council’s body of work to benchmark the state of data management for both business and data leaders, and understand how trusted data functions and capabilities are evolving in our data-driven, increasingly complex world,” said John Bottega, president of EDM Council.
New framework lays out parameters for cloud data management
EDM Council’s inaugural survey also highlights the 14 key cloud data management controls that are a key part of the Council’s new Cloud Data Management Capabilities framework. The poll included questions asking respondents to indicate whether their processes in each of the 14 areas are manual, automated or not implemented (Figure A).
Figure A
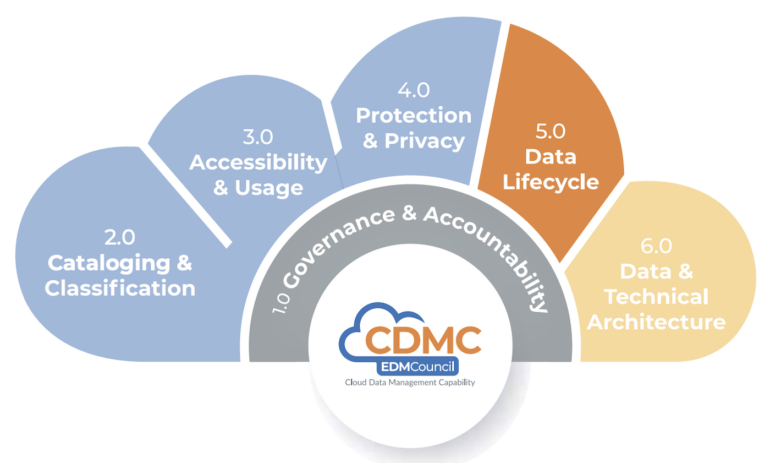
EDM Council said its CDMC framework was developed over 18 months with some 300 individuals from 100 firms, including cloud providers Amazon Web Services, Google, IBM and Microsoft. It was, said EDM, designed to outline the “best practices and capabilities that help organizations ensure seamless cloud migration, effective data protection, and robust data management in the cloud” and includes requirements for governance and accountability, cataloging and classification and accessibility and use of sensitive data.
SEE: Top six Linux distributions for your data center (TechRepublic)
The Council suggested several ways of improving data management for organizations moving capabilities and storage to cloud services. They should:
- Prioritize automation for cloud data management.
- Focus on implementing controls that are currently absent, especially for cost metrics and data lineage.
- Prioritize security controls.
The study authors wrote, “All stakeholders should have a clear understanding of data controls and accountability for each role. The approach is similar to how data governance, controls, and accountability are applied to conventional data management in an organization.”
“Cloud adoption requires comprehensive data management capabilities, including data risk controls and automation, to ensure that data is protected and controlled to meet regulatory requirements across jurisdictions,” said Diana Ascher, EDM Council’s head of research. “The report outlines where greater attention should be directed to ensure data assets are central to planning and executing trusted cloud strategies.”
[ad_2]
Source link



