[ad_1]
The consulting agency PricewaterhouseCoopers not too long ago revealed classes discovered from the disruptive and dear ransomware assault in Could 2021 on Eire’s public well being system. The unusually candid autopsy discovered that almost two months elapsed between the preliminary intrusion and the launching of the ransomware. It additionally discovered affected hospitals had tens of hundreds of outdated Home windows 7 programs, and that the well being system’s IT directors failed to reply to a number of warning indicators {that a} large assault was imminent.

PWC’s timeline of the times main as much as the deployment of Conti ransomware on Could 14.
Eire’s Well being Service Govt (HSE), which operates the nation’s public well being system, acquired hit with Conti ransomware on Could 14, 2021. A timeline within the report (above) says the preliminary an infection of the “affected person zero” workstation occurred on Mar. 18, 2021, when an worker on a Home windows laptop opened a booby-trapped Microsoft Excel doc in a phishing e mail that had been despatched two days earlier.
Lower than per week later, the attacker had established a dependable backdoor connection to the worker’s contaminated workstation. After infecting the system, “the attacker continued to function within the atmosphere over an eight week interval till the detonation of the Conti ransomware on Could 14, 2021,” the report states.
Based on PWC’s report (PDF), there have been a number of warnings a few critical community intrusion, however these crimson flags had been both misidentified or not acted on shortly sufficient:
- On Mar. 31, 2021, the HSE’s antivirus software program detected the execution of two software program instruments generally utilized by ransomware teams — Cobalt Strike and Mimikatz — on the Affected person Zero Workstation. However the antivirus software program was set to observe mode, so it didn’t block the malicious instructions.”
- On Could 7, the attacker compromised the HSE’s servers for the primary time, and over the following 5 days the intruder would compromise six HSE hospitals. On Could 10, one of many hospitals detected malicious exercise on its Microsoft Home windows Area Controller, a crucial “keys to the dominion” element of any Home windows enterprise community that manages person authentication and community entry.
- On 10 Could 2021, safety auditors first recognized proof of the attacker compromising programs inside Hospital C and Hospital L. Hospital C’s antivirus software program detected Cobalt Strike on two programs however did not quarantine the malicious recordsdata.
- On Could 13, the HSE’s antivirus safety supplier emailed the HSE’s safety operations staff, highlighting unhandled risk occasions relationship again to Could 7 on at the least 16 programs. The HSE Safety Operations staff requested that the Server staff restart servers.
By then it was too late. At simply after midnight Eire time on Could 14, the attacker executed the Conti ransomware inside the HSE. The assault disrupted services at several Irish hospitals and resulted within the close to full shutdown of the HSE’s nationwide and native networks, forcing the cancellation of many outpatient clinics and healthcare companies. The variety of appointments in some areas dropped by as much as 80 p.c.”
Conti initially demanded USD $20 million value of digital forex in change for a digital key to unlock HSE servers compromised by the group. However maybe in response to the general public outcry over the HSE disruption, Conti reversed course and gave the HSE the decryption keys with out requiring cost.
Nonetheless, the work to revive contaminated programs would take months. The HSE finally enlisted members of the Irish army to herald laptops and PCs to assist restore laptop programs by hand. It wasn’t till September 21, 2021 that the HSE declared 100% of its servers had been decrypted.
As dangerous because the HSE ransomware assault was, the PWC report emphasizes that it may have been far worse. For instance, it’s unclear how a lot knowledge would have been unrecoverable if a decryption key had not change into out there because the HSE’s backup infrastructure was solely periodically backed as much as offline tape.
The assault additionally may have been worse, the report discovered:
- if there had been intent by the Attacker to focus on particular units inside the HSE atmosphere (e.g. medical units);
- if the ransomware took actions to destroy knowledge at scale;
- if the ransomware had auto-propagation and persistence capabilities, for instance through the use of an exploit to propagate throughout domains and trust-boundaries to medical units (e.g. the EternalBlue exploit utilized by the WannaCry and NotPetya15 assaults);
- if cloud programs had additionally been encrypted such because the COVID-19 vaccination system
The PWC report accommodates quite a few suggestions, most of which focus on hiring new personnel to guide the group’s redoubled safety efforts. However it’s clear that the HSE has an infinite quantity of labor forward to grow in security maturity. For instance, the report notes the HSE’s hospital community had over 30,000 Home windows 7 workstations that had been deemed finish of life by the seller.
“The HSE assessed its cybersecurity maturity ranking as low,” PWC wrote. “For instance, they don’t have a CISO or a Safety Operations Middle established.”
PWC additionally estimates that efforts to construct up the HSE’s cybersecurity program to the purpose the place it could actually quickly detect and reply to intrusions are prone to price “a a number of of the HSE’s present capital and operation expenditure in these areas over a number of years.”
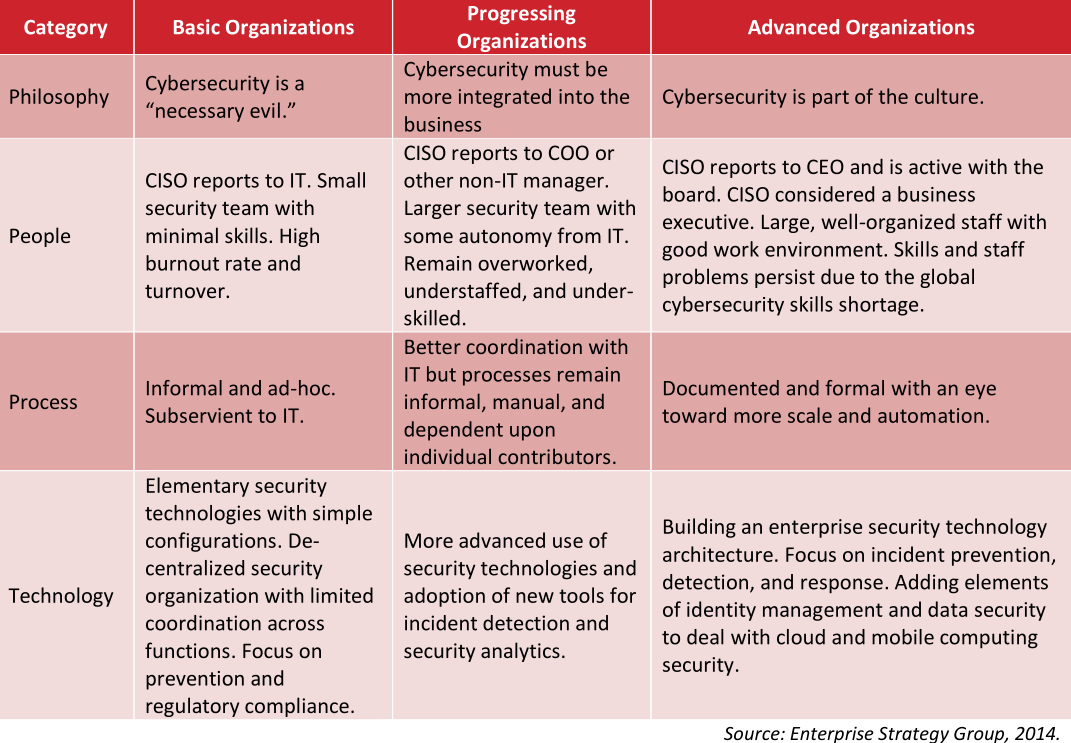
One thought of a “safety maturity” mannequin.
In June 2021, the HSE’s director common stated the restoration prices for the Could ransomware assault were likely to exceed USD $600 million.
What’s exceptional about this incident is that the HSE is publicly funded by the Irish authorities, and so in principle it has the cash to spend (or elevate) to pay for all these bold suggestions for growing their safety maturity.
That stands in stark distinction to the healthcare system right here in america, the place the one largest obstacle to doing safety nicely continues to be lack of constructing it an actual finances precedence. Additionally, most healthcare organizations in america are non-public corporations that function on razor-thin revenue margins.
I do know this as a result of in 2018 I used to be requested to provide the keynote at an annual gathering of the Healthcare Data Sharing and Evaluation Group (H-ISAC), an trade group centered on sharing details about cybersecurity threats. I nearly didn’t settle for the invitation: I’d written little or no about healthcare safety, which appeared to be dominated by protection of whether or not healthcare organizations complied with the letter of the regulation in america. That compliance centered on the Health Insurance Portability and Accountability Act (HIPAA), which prioritizes defending the integrity and privateness of affected person knowledge.
To rise up to hurry, I interviewed over a dozen of the healthcare safety trade’s greatest and brightest minds. A typical chorus I heard from these interviewed was that if it was security-related however didn’t must do with compliance, there most likely wasn’t a lot probability it might get any finances.
These sources unanimously stated that nevertheless well-intentioned, it’s not clear that the “shield the info” regulatory method of HIPPA was working from an total risk perspective. Based on HealthcareIT News, greater than 40 million affected person data have been compromised in incidents reported to the federal authorities in 2021 to this point alone.
Throughout my 2018 speak, I attempted to emphasise the first significance of having the ability to reply shortly to intrusions. Right here’s a snippet of what I instructed that H-ISAC viewers:
“The time period ‘Safety Maturity’ refers back to the road smarts of a person or group, and this maturity typically comes from making loads of errors, getting hacked so much, and hopefully studying from every incident, measuring response instances, and bettering.
Let me say up entrance that every one organizations get hacked. Even ones which might be doing every part proper from a safety perspective get hacked most likely on daily basis in the event that they’re sufficiently big. By hacked I imply somebody inside the group falls for a phishing rip-off, or clicks a malicious hyperlink and downloads malware. As a result of let’s face it, it solely takes one screw up for the hackers to get a foothold within the community.
Now that is in itself isn’t dangerous. Until you don’t have the aptitude to detect it and reply shortly. And if you happen to can’t try this, you run the intense danger of getting a small incident metastasize right into a a lot bigger downside.
Consider it just like the medical idea of the ‘Golden Hour:’ That brief window of time instantly following a traumatic harm like a stroke or coronary heart assault during which life-saving medication and a spotlight is prone to be simplest. The identical idea holds true in cybersecurity, and it’s precisely why so many organizations nowadays are inserting extra of their sources into incident response, as a substitute of simply prevention.”
America’ considerably decentralized healthcare system implies that many ransomware outbreaks are usually restricted to regional or native healthcare amenities. However a well-placed ransomware assault or collection of assaults may inflict critical injury on the sector: A December 2020 report from Deloitte says the highest 10 well being programs now management a 24 p.c market share and their income grew at twice the speed of the remainder of the market.
In October 2020, KrebsOnSecurity broke the story that the FBI and U.S. Division of Homeland Safety had obtained chatter from a high ransomware group which warned of an “imminent cybercrime risk to U.S. hospitals and healthcare suppliers.” Members related to the Russian-speaking ransomware group often called Ryuk had mentioned plans to deploy ransomware at greater than 400 healthcare amenities in america.
Hours after that piece ran, I heard from a revered H-ISAC safety skilled who questioned whether or not it was value getting the general public so riled up. The story had been up to date a number of instances all through the day, and there have been at the least 5 healthcare organizations hit with ransomware inside the span of 24 hours.
“I assume it might assist if I understood what the baseline is, like what number of healthcare organizations get hit with ransomware on common in a single week?” I requested the supply.
“It’s extra like one a day,” the supply confided.
In all probability, the HSE will get the cash it must implement the packages really helpful by PWC, nevertheless lengthy that takes. I ponder what number of U.S.-based healthcare organizations may say the identical.
[ad_2]
Source link



