[ad_1]
Communications large T-Cellular mentioned as we speak it’s investigating the extent of a breach that hackers declare has uncovered delicate private knowledge on 100 million T-Cellular USA clients, in lots of instances together with the title, Social Safety quantity, handle, date of delivery, cellphone quantity, safety PINs and particulars that uniquely establish every buyer’s cell system.
On Sunday, Vice.com broke the news that somebody was promoting knowledge on 100 million folks, and that the info got here from T-Cellular. In a statement revealed on its web site as we speak, the corporate confirmed it had suffered an intrusion involving “some T-Cellular knowledge,” however mentioned it was too quickly in its investigation to know what was stolen and what number of clients may be affected.
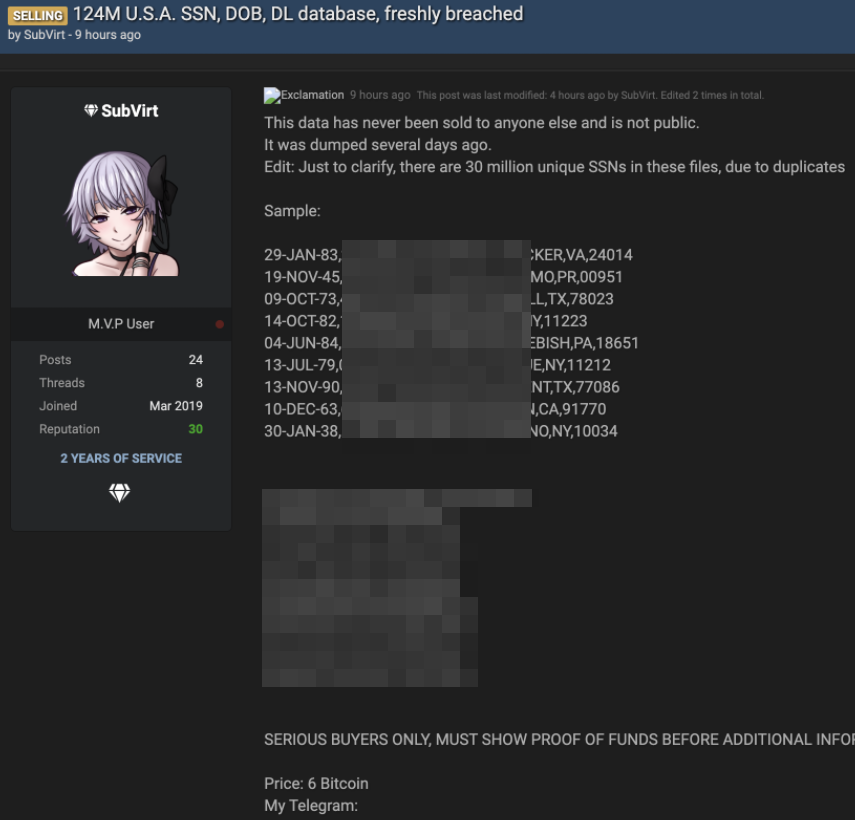
A gross sales thread tied to the allegedly stolen T-Cellular buyer knowledge.
“Now we have decided that unauthorized entry to some T-Cellular knowledge occurred, nevertheless we have now not but decided that there’s any private buyer knowledge concerned,” T-Cellular wrote.
“We’re assured that the entry level used to achieve entry has been closed, and we’re persevering with our deep technical overview of the scenario throughout our techniques to establish the character of any knowledge that was illegally accessed,” the assertion continued. “This investigation will take a while however we’re working with the best diploma of urgency. Till we have now accomplished this evaluation we can’t verify the reported variety of data affected or the validity of statements made by others.”
The intrusion got here to mild on Twitter when the account @und0xxed began tweeting the small print. Reached through direct message, Und0xxed mentioned they weren’t concerned in stealing the databases however was as an alternative accountable for discovering consumers for the stolen T-Cellular buyer knowledge.
Und0xxed mentioned the hackers discovered a gap in T-Cellular’s wi-fi knowledge community that allowed entry to 2 of T-Cellular’s buyer knowledge facilities. From there, the intruders have been capable of dump a lot of buyer databases totaling greater than 100 gigabytes.
They declare a kind of databases holds the title, date of delivery, SSN, drivers license info, plaintext safety PIN, handle and cellphone variety of 36 million T-Cellular clients in the USA — all going again to the mid-Nineteen Nineties.
The hacker(s) declare the purloined knowledge additionally consists of IMSI and IMEI data for 36 million clients. These are distinctive numbers embedded in buyer cell gadgets that establish the system and the SIM card that ties that buyer’s system to a phone quantity.
“If you wish to confirm that I’ve entry to the info/the info is actual, simply give me a T-Cellular quantity and I’ll run a lookup for you and return the IMEI and IMSI of the cellphone at the moment connected to the quantity and some other particulars,” @und0xxed mentioned. “All T-Cellular USA pay as you go and postpaid clients are affected; Dash and the opposite telecoms that T-Cellular owns are unaffected.”
Different databases allegedly accessed by the intruders included one for pay as you go accounts, which had far fewer particulars about clients.
“Pay as you go clients often are simply cellphone quantity and IMEI and IMSI,” Und0xxed mentioned. “Additionally, the gathering of databases consists of historic entries, and lots of cellphone numbers have 10 or 20 IMEIs connected to them over time, and the service dates are supplied. There’s additionally a database that features bank card numbers with six digits of the playing cards obfuscated.”
T-Cellular declined to remark past what the corporate mentioned in its weblog put up as we speak.
In 2015, a pc breach at massive three credit score bureau Experian exposed the Social Security numbers and other data on 15 million people who applied for financing from T-Mobile.
Like different cell suppliers, T-Cellular is locked in a relentless battle with scammers who goal its personal staff in SIM swapping attacks and different strategies to wrest management over worker accounts that may present backdoor entry to buyer knowledge. In at the very least one case, retail retailer staff have been complicit within the account takeovers.
WHO HACKED T-MOBILE?
The Twitter profile for the account @Und0xxed features a shout out to @IntelSecrets, the Twitter account of a reasonably elusive hacker who additionally has passed by the handles IRDev and V0rtex. Requested if @IntelSecrets was concerned within the T-Cellular intrusion, @und0xxed confirmed that it was.
The IntelSecrets nicknames correspond to a person who has claimed duty for modifying the supply code for the Mirai “Internet of Things” botnet to create a variant referred to as “Satori,” and supplying it to others who used it for felony acquire and have been later caught and prosecuted. Like Kenny “NexusZeta” Schuchmann, who pleaded guilty in 2019 to working the Satori botnet. Two different younger males have been charged in connection with Satori — however not IntelSecrets.
How do we all know all this about IntelSecrets/IRDev/V0rtex? That id has acknowledged as a lot in a sequence of weird lawsuits filed by an individual who claims their actual title is John Erin Binns. The identical Binns id operates the web site intelsecrets[.]su.
On that web site, Binns claims he fled to Germany and Turkey to evade prosecution within the Satori case, solely to be kidnapped in Turkey and subjected to numerous types of psychological and bodily torture. Based on Binns, the U.S. Central Intelligence Company (CIA) falsely instructed their counterparts in Turkey that he was a supporter or member of the Islamic State (ISIS), a declare he says led to his alleged seize and torture by the Turks.
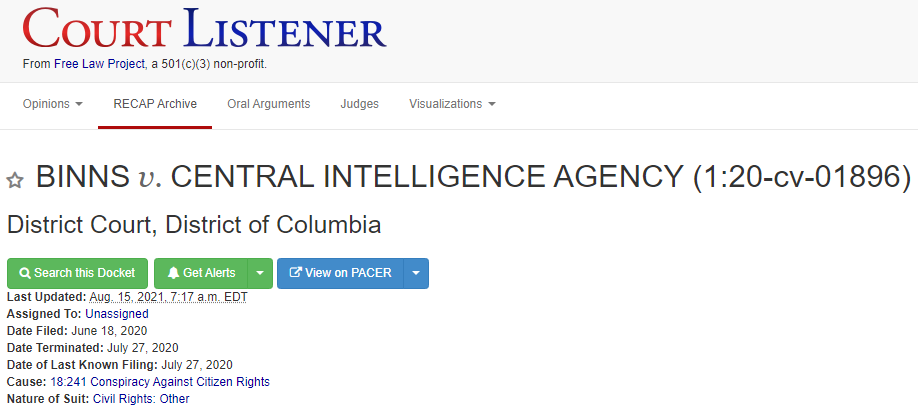
Since then, Binns has filed a flood of lawsuits naming varied federal businesses — together with the FBI, the CIA, and the U.S. Special Operations Command (PDF), demanding that the federal government flip over info collected about him and looking for restitution for his alleged kidnapping by the hands of the CIA.
Talking to the researcher Alon Gal (@underthebreach), the hackers answerable for the T-Cellular intrusion mentioned they did it to “retaliate towards the US for the kidnapping and torture of John Erin Binns in Germany by the CIA and Turkish intelligence brokers in 2019. We did it to hurt US infrastructure.”
Replace, Aug. 18, 9:15 a.m. ET: In a weblog put up Monday night, T-Cellular acknowledged {that a} knowledge breach has uncovered the names, date of delivery, Social Safety quantity and driver’s license/ID info of greater than 40 million present, former or potential clients.
[ad_2]
Source link



